Your Cloud Server’s Digital Bouncer
Imagine your Google Cloud Virtual Machine (VM) as a high-security building. While you’ve carefully chosen its location and equipped it with powerful internal systems, it still needs a robust security detail at its entrance and exits. This is precisely the role of Google Cloud Firewall Policies: they act as digital bouncers, meticulously controlling who (or what) gets in and out of your servers. Neglecting these policies is like leaving your building’s doors wide open in a busy city like Chandigarh—a huge risk. In the vast and often unpredictable landscape of the internet, a misconfigured firewall is an open invitation for malicious actors, data breaches, and service disruptions. This guide will demystify Google Cloud’s powerful firewall capabilities, showing you how to implement effective rules that protect your valuable cloud resources, maintain service integrity, and ensure your applications run securely. We’ll explore practical scenarios, real-world best practices, and the strategic importance of this fundamental security layer.
Crafting Your Security Rules
Understanding Google Cloud Firewall Rules: The Essentials
Google Cloud Firewall rules operate at the network level, governing traffic to and from your VM instances. They are crucial for isolating your applications, restricting access, and preventing unauthorized communication. Unlike traditional on-premise firewalls, Google Cloud’s firewalls are highly scalable, integrated directly into your Virtual Private Cloud (VPC) network, and managed centrally.
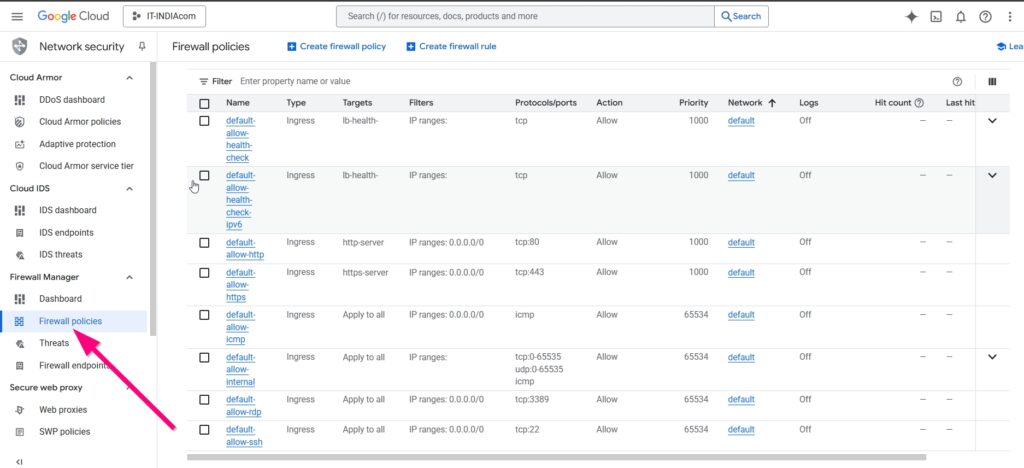
Key components of a firewall rule include:
- Direction: Whether the rule applies to Ingress (incoming) or Egress (outgoing) traffic.
- Action: `Allow` or `Deny` traffic matching the rule.
- Targets: Which VMs the rule applies to (e.g., all VMs in a network, specific VMs by tag or service account).
- Source/Destination Filters: IP ranges (CIDR blocks) or service accounts that traffic must originate from or be destined for.
- Protocols and Ports: The specific communication protocols (e.g., TCP, UDP, ICMP) and port numbers (e.g., 22 for SSH, 80 for HTTP, 443 for HTTPS).
A fundamental best practice is the “principle of least privilege.” This means you should only open ports and allow traffic that is absolutely necessary for your applications to function. For instance, if your web server only serves HTTP and HTTPS, there’s no need to open all ports. You can find comprehensive documentation on how these rules work on the Google Cloud VPC firewall rules page.
Real-World Scenarios: Protecting Your Applications
Let’s consider practical examples where firewall rules are indispensable:
- Web Server Security (HTTP/HTTPS): For a public-facing website hosted on your VM, you need to allow inbound traffic on ports 80 (HTTP) and 443 (HTTPS) from all IP addresses (
0.0.0.0/0). All other inbound traffic should be denied by default. - SSH Access (Remote Management): To securely manage your VM, you should allow SSH traffic (port 22, or a custom port as discussed in our server hardening guide) only from your specific office or home IP address. This significantly reduces the attack surface.
- Database Isolation: If you have a separate VM for your MySQL database (as we explored in our guide on moving databases), you should only allow inbound traffic on port 3306 (MySQL) from your application server’s internal IP address, not from the public internet.
- Outgoing Traffic Control: While often overlooked, controlling egress traffic is also vital. You might deny all outgoing traffic except for specific ports needed for updates, API calls, or monitoring tools. This prevents a compromised server from communicating with malicious external command-and-control servers.
These targeted rules ensure that your services are accessible only to legitimate users and other authorized services, effectively creating a digital perimeter around each of your VMs. For deeper dives into advanced network security, Google often shares insights on their Google Cloud Security Twitter account.
Stats & Case Studies – The Cost of Neglect
The consequences of weak firewall policies are stark and well-documented. Cybersecurity Ventures estimates that cybercrime will cost the world $10.5 trillion annually by 2025. A significant portion of these costs stems from vulnerabilities that could have been mitigated by robust firewall rules. For instance:
- Ransomware Attacks: Many ransomware variants gain initial access through publicly exposed and unpatched services, or through unsecured RDP/SSH ports. Proper ingress rules can block these entry points.
- Data Exfiltration: Compromised servers can silently transmit sensitive data out of your network. Egress firewall rules can detect and block unauthorized outbound communication, acting as a critical last line of defense.
- DDoS Attacks: While Google Cloud offers advanced DDoS protection, intelligently configured firewall rules can help mitigate the impact of certain volumetric attacks by blocking traffic from known malicious IP ranges or unusual patterns.
A recent high-profile case involved a cloud environment where a database server was left exposed to the internet. Attackers quickly exploited a known vulnerability, leading to a significant data breach. This scenario is preventable with a simple firewall rule that restricts database access to internal application servers only. Such incidents highlight that even a single misconfigured rule can have cascading effects, leading to substantial financial, reputational, and operational damage. Google Cloud continuously invests in security and provides tools to help prevent these scenarios, as detailed in their cloud security whitepapers.
The Takeaway – Build a Resilient Cloud Environment
Implementing effective Google Cloud Firewall Policies is a fundamental, non-negotiable step in securing your Virtual Machines. By meticulously defining who can communicate with your servers and how, you build a resilient defense against the ever-present threats of the digital world. Remember the principle of least privilege: only allow what’s absolutely necessary. Combine these firewall rules with other hardening techniques, such as strong SSH configurations and regular software updates (as detailed in our article “Securing Your Fresh Ubuntu Server on Google Cloud”), to create a layered security approach. Proactive security management is not just a best practice; it’s an investment in the stability, integrity, and future success of your cloud infrastructure. What’s your biggest challenge when configuring firewalls in the cloud?
To avoid unexpected charges, you should:
- Monitor your usage in the Google Cloud console.
- Set up billing alerts to notify you when your spending reaches a certain threshold.
- Review the pricing page for the specific services you plan to use before you start.
✍️ Need Content Like This?
We craft high-quality, SEO-optimized articles tailored for blogs, news sites, and educational platforms. If you enjoy thoughtful writing and open-source spirit, just buy me a coffee and I’ll write 1,000 words for you. Let’s build something meaningful together. Contact us to get started.

